
[vc_row bg_type=”” dima_canvas_style=”” translate_x=”0″ dima_z_index=”0″ delay=”” delay_duration=”” delay_offset=””][vc_column min_height=”” bg_type=”” dima_canvas_style=”” translate_x=”0″ dima_z_index=”0″ delay=”” delay_duration=”” delay_offset=”” width=”1/1″][text]Have you experienced frustration or weariness from the repeated use of Multi-Factor Authentication (MFA) when accessing your accounts? Chances are high you have experienced MFA Fatigue.
Passwords were once considered the best protection with user accounts. Having faced many challenges, the development of Multi-Factor Authentication was prompted to add an extra layer of defense. However, as organizations strengthen their security measures, attackers adapt, giving rise to a concerning phenomenon known as MFA fatigue attacks.
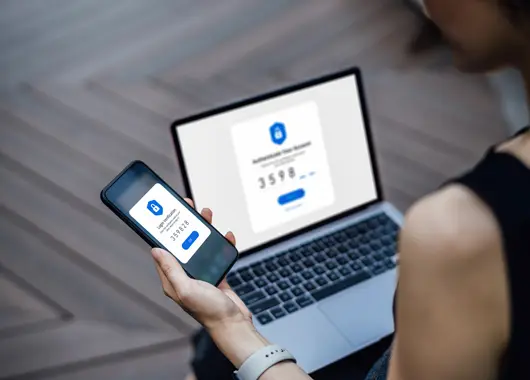
MFA Fatigue attacks, also called authentication bombing, exploit the human factor in cybersecurity. These attacks aim to overwhelm the target by bombarding them with repeated two-factor authentication requests via email, phone, or registered devices. The goal is to induce frustration or fatigue in the victim, leading them to unwittingly grant access to the attacker.
Attackers initiate MFA fatigue attacks through various means, such as phishing emails or insider threats. Once the attacker gains the target’s credentials, they flood the victim with push notifications for two-factor authentication. In a recent incident, an attacker posed as tech support, exploiting the user’s authentication process, and tricking them into approving the flood of authentication prompts.
Increasing number of online accounts is a factor contributing to the rise of MFA fatigue attacks. The surge in online accounts across various services has made users more susceptible to MFA fatigue attacks. The effectiveness of this tactic certainly doesn’t help either. MFA fatigue attacks capitalize on users’ tendencies to click on multiple notifications, assuming there’s a glitch, especially when the requests seem to come from trusted systems. Weaknesses in MFA systems, such as a lack of strict location verification during login, contribute to the success of these attacks. Additionally, the ease with which MFA fatigue attacks can be automated allows attackers to target a broader range of victims.
As redundant as it may sound, don’t click on anything you don’t recognize. By using strong, unique passwords and having MFA enabled, you get an additional layer of security. But make sure to stay informed about phishing tactics, as MFA fatigue attacks often involve phishing.
To enhance defense against MFA fatigue attacks, individual users can implement the following strategies:
MFA fatigue attacks represent a significant threat to organizations, requiring a proactive and multifaceted approach to defense. By implementing the above strategies, users can significantly strengthen their defenses against MFA fatigue attacks and ensure a more secure authentication process. Remember, never approve an MFA prompt you didn’t initiate.[/text][/vc_column][/vc_row]

